Outsourcing the Constitution
Private Infrastructure and the Quiet Expansion of State Power
Policy Analysis
By Christopher Rixman | The Honey Badger Journal
The architecture of surveillance in the United States is not expanding through dramatic new legislation. There has been no singular vote to repeal privacy protections, no sweeping constitutional amendment dismantling the Fourth Amendment. On paper, the legal framework governing search, seizure, and warrants remains intact.
But the operational environment surrounding those protections has changed.
Surveillance authority today is expanding not primarily through statute, but through procurement, platform integration, policy reinterpretation, and private-sector infrastructure. The result is a monitoring ecosystem where the functional capacity to track, infiltrate, and analyze populations grows continuously — even as constitutional doctrine appears formally unchanged.
To understand the shift, it helps to look at several recent developments that, at first glance, appear unrelated.
Together, they form a structural pattern.
Ken Klippenstein’s reporting on Department of Homeland Security policy revealed the expansion of what officials call “masked engagement,” a surveillance authority that allows federal agents to enter digital communities under assumed identities. As Klippenstein reported, DHS policy now authorizes agents to conduct online infiltration using identities that “conceal government affiliation,” enabling officers to join private groups, friend targets, and interact within restricted online spaces without triggering full undercover authorization protocols.
The distinction is bureaucratic, but the implications are operational. Entry into private digital environments — once gated behind higher investigative thresholds — now occurs through a middle-tier authority category whose limits remain loosely defined.
Surveillance access expands not by eliminating oversight outright, but by reclassifying the activity beneath it.
At the same time, Glenn Greenwald’s analysis of consumer surveillance infrastructure highlighted how corporate technologies are transforming the monitoring landscape from the outside in. Amazon’s promotion of its Ring camera network demonstrated how millions of privately owned devices can be linked into searchable, neighborhood-wide monitoring systems. What consumers purchase as individual home-security products increasingly function as interoperable surveillance grids.
Greenwald’s broader point is that consumer technology is transforming private life into searchable infrastructure. When millions of cameras are networked, the capability stops being “one homeowner watching their porch” and starts resembling a distributed monitoring grid. Privacy advocates have warned that linking consumer devices through AI search functions pushes biometric identification down into everyday technology, often without meaningful public consent or oversight.
The infrastructure is privately owned, but the surveillance capability is collective.
A second Greenwald case underscored how data retention further complicates public privacy assumptions. In reporting on the disappearance of Nancy Guthrie, investigators were able to retrieve footage from a Google Nest camera system that users believed did not store video without an active subscription. The discovery reinforced a principle long understood by cybersecurity professionals: data assumed to be temporary is often retained in ways opaque to the public.
As one cybersecurity expert summarized in response to the retrieval: “Data is never deleted — it’s just renamed.”
Expectations of privacy, in other words, are being shaped by user interface design and marketing language rather than technical reality.
Overlay those developments with operational enforcement activity, and the structural convergence becomes clearer. Reporting from Drop Site News documented large-scale federal immigration enforcement deployments involving thousands of agents across major metropolitan areas, alongside mounting scrutiny over detention conditions and operational conduct. Oversight findings tied to these operations described some facilities as overcrowded and degrading, underscoring the scale and intensity of enforcement activity now underway.
Mass enforcement requires mass information.
When viewed together, these developments outline a surveillance ecosystem expanding across multiple institutional layers simultaneously. Federal agencies broaden digital infiltration authorities. Private technology platforms build networked monitoring infrastructures. Enforcement operations operationalize the intelligence produced by both.
Each component can be justified independently. Undercover engagement has long existed in law enforcement. Home security systems are legal consumer products. Immigration enforcement falls within federal jurisdiction.
But constitutional tension emerges at the level of integration.
The Fourth Amendment regulates government search authority, requiring warrants supported by probable cause. Yet much of today’s surveillance capacity originates outside direct government collection. Data is generated by private platforms, stored on corporate servers, and accessed through legal mechanisms distinct from traditional warrants. Monitoring infrastructure is purchased voluntarily by citizens and later integrated into investigative workflows.
Surveillance, in effect, is being outsourced.
The legal doctrine has not disappeared. It has been routed around.
Speech Infrastructure and the Outsourcing of the First Amendment
The same outsourcing dynamic is now visible in the speech environment.
Free speech restrictions in the United States do not always arrive through legislation. Increasingly, they operate through platform governance, ownership pressure, and moderation infrastructure sitting inside private hands aligned with state interests.
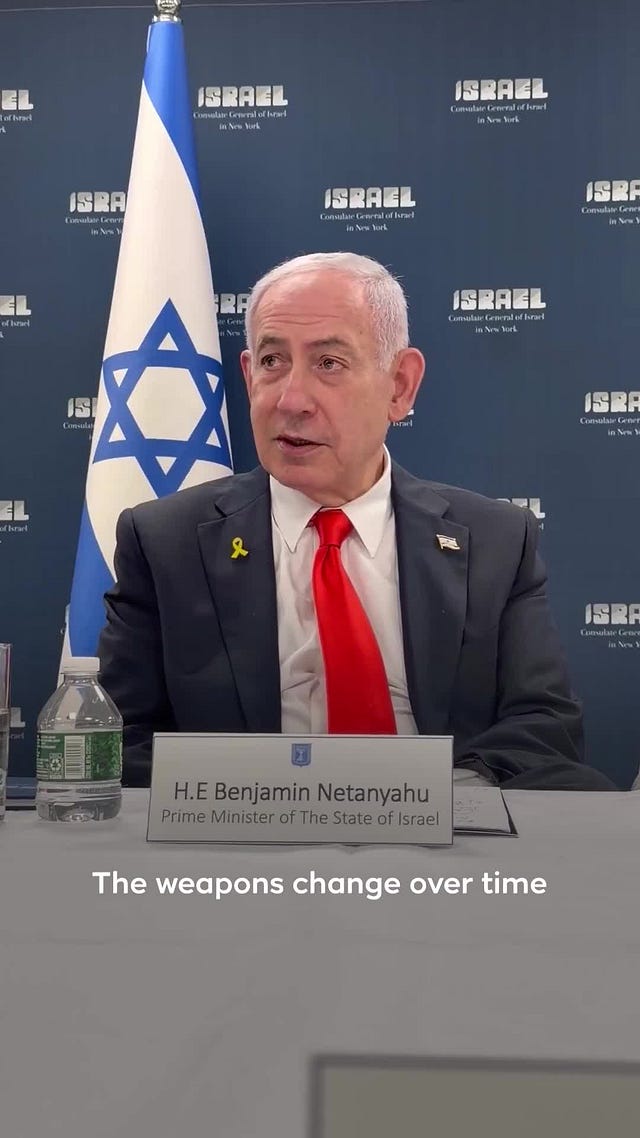
During the Gaza war information cycle, Israeli Prime Minister Benjamin Netanyahu publicly framed TikTok as a strategic narrative threat. In public remarks and interviews, Netanyahu warned that the platform was shaping global opinion against Israel, particularly among younger audiences consuming frontline footage.
 Tiktok failed to load.
Tiktok failed to load.Enable 3rd party cookies or use another browser
Anti-Defamation League director Jonathan Greenblatt echoed the concern, describing TikTok as one of the most influential platforms driving negative international perception of Israeli military operations.
The concern was not about data security alone.
It was about narrative power.
TikTok had become one of the primary platforms where Palestinian journalists, civilians, and influencers were documenting wartime conditions in real time, often bypassing Western media framing filters.
Shortly after these pressure campaigns intensified, political and corporate attention turned toward TikTok’s ownership structure. U.S. lawmakers escalated divestment demands tied to national security concerns around Chinese ownership.
At the corporate level, figures like Oracle billionaire Larry Ellison — a major U.S. defense contractor partner and Israeli technology investor — entered acquisition consortium discussions tied to TikTok’s potential restructuring alongside American investors.
Simultaneously, Palestinian creators began reporting mass content removals, account suspensions, and algorithmic suppression during peak wartime visibility windows. Large documentation accounts reported takedowns within hours or days of posting battlefield or humanitarian footage.
Whether each moderation decision was automated, policy-driven, or complaint-triggered remains difficult to externally verify.
But the structural effect was measurable:
Palestinian narrative distribution narrowed during peak global attention.
This is where First Amendment tension emerges structurally rather than legally.
The government does not need to pass censorship laws if speech visibility is governed by private infrastructure operating inside geopolitical pressure environments.
If allies of the state hold influence over platform governance, speech constraints can be implemented infrastructurally rather than legislatively.
No law gets passed.
No court reviews it.
But speech distribution shifts anyway.
Rights on Paper, Power in Practice
None of these mechanisms alone nullifies constitutional protections.
Collectively, they reconfigure the environment in which those protections function.
When law enforcement accesses privately collected surveillance data, constitutional thresholds operate differently. When agents enter digital communities through policy-defined engagement categories rather than court-authorized infiltration, oversight operates differently. When consumer technology networks create persistent monitoring environments, anonymity expectations erode.
When speech distribution is governed by privately owned platforms operating under geopolitical pressure, First Amendment friction is displaced into corporate policy frameworks.
The result is a constitutional environment where rights formally remain — but enforcement triggers grow harder to locate.
The architecture expands quietly, bureaucratically, procedurally.
No singular vote authorizes it.
No singular policy announces it.
Capacity grows through procurement contracts, platform capabilities, policy revisions, ownership structures, and enforcement integration.
From an institutional design standpoint, it is efficient.
From a civil liberties standpoint, it introduces unresolved tension.
Because if surveillance and speech governance operate through outsourced infrastructure rather than direct state action, constitutional safeguards encounter the state less often at the point where they are legally activated.
The Fourth Amendment still exists.
The First Amendment still exists.
But the enforcement architecture surrounding both no longer needs to approach through the front door.
It can log in instead.
Works Cited
Klippenstein, Ken — “Exclusive: ICE Masks Up in More Ways Than One” (Substack investigative reporting on DHS masked engagement policy)
Greenwald, Glenn — Ring surveillance infrastructure & Nest data retention analysis
Drop Site News — Federal immigration enforcement surge reporting
Electronic Frontier Foundation — Biometric surveillance warnings
CBS News — Nancy Guthrie Nest camera footage retrieval reporting
U.S. Department of Homeland Security — Online engagement policy guidance





